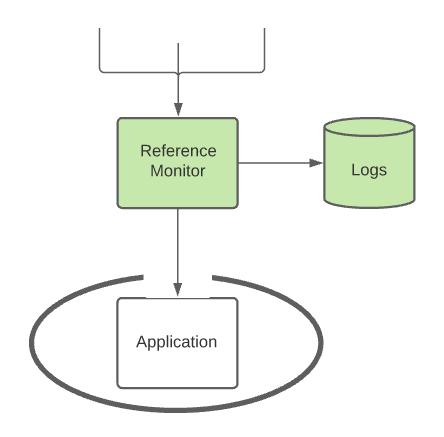
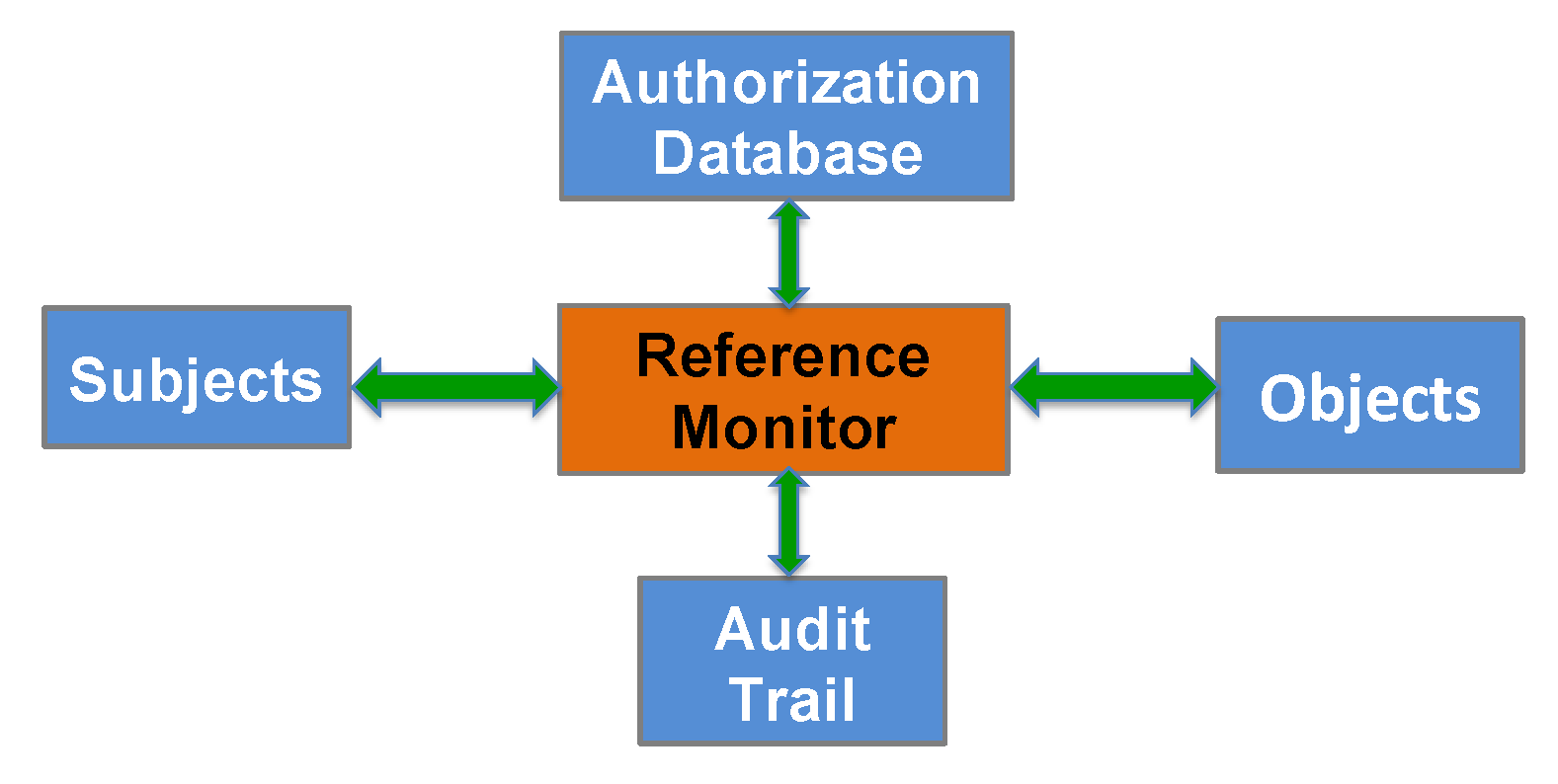
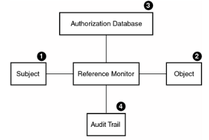
A system's security architecture. The reference monitor intercepts each... | Download Scientific Diagram

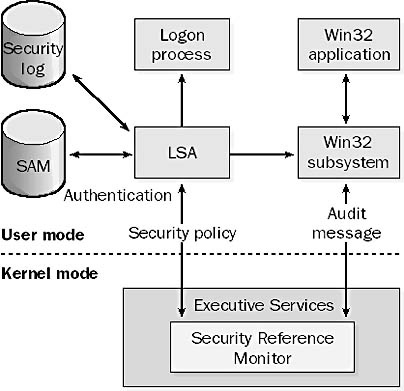
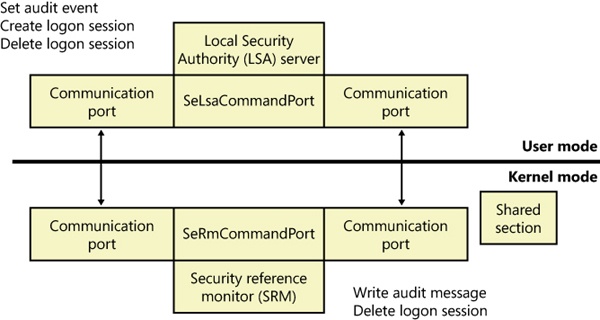
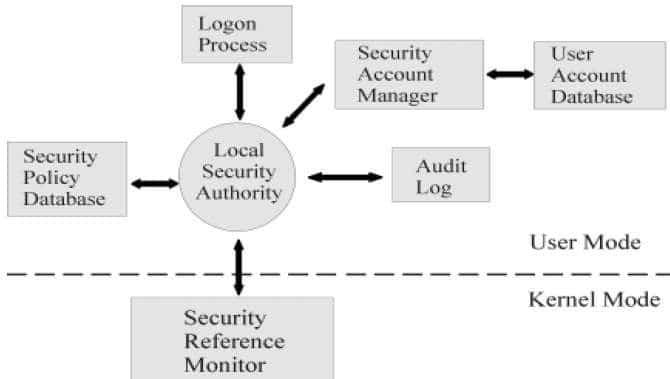
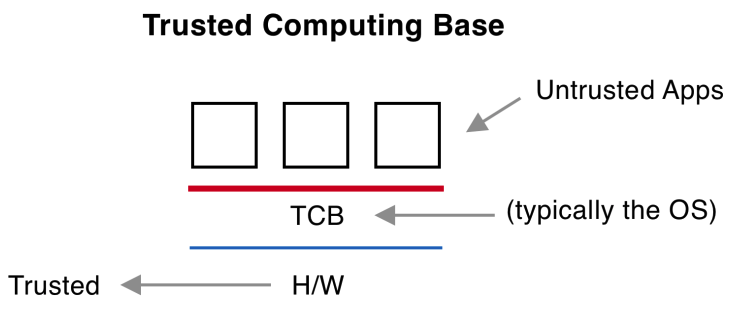
Security kernels implement and enforce the reference monitor concept. The security kernel is used to build the trusted computing system. Security kernels have four main requirements. Which of these is NOT included
GitHub - garagakteja/Reference-Monitor-Security-Build: Restricted Python (Repy) based hands-on implementation of Security Mechanisms and Access control

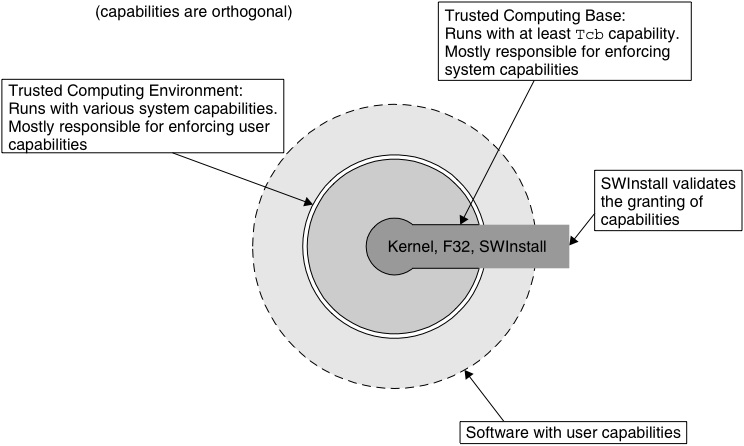

![PDF] Teaching the security mindset with reference monitors | Semantic Scholar PDF] Teaching the security mindset with reference monitors | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/9733b37e5b61ccff306b21907abd3143995c1f8b/2-Figure1-1.png)