
BEGINEER'S CRASH COURSE FOR FINDING ACCESS CONTROL VULNERABILITIES IN THE WEB APPS:PART 1 | by Cyber Defecers | InfoSec Write-ups
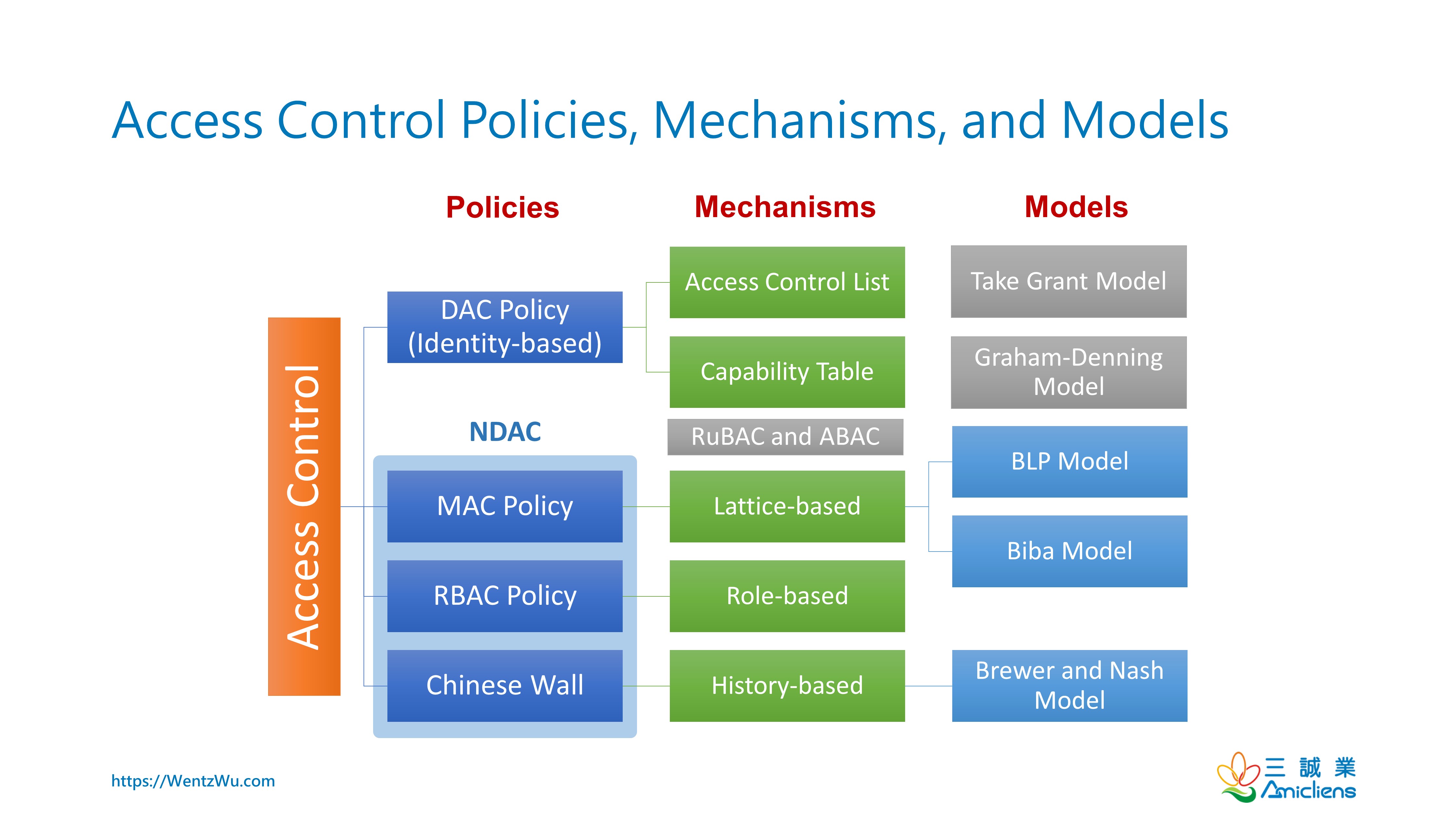
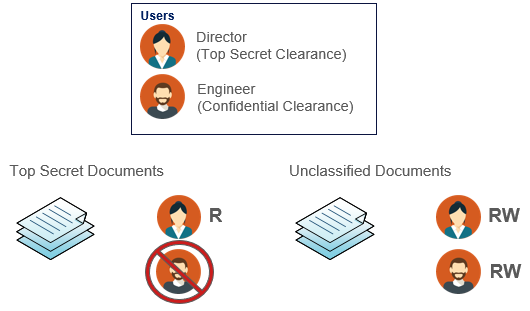
Discretionary and Non-Discretionary Access Control Policies by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu









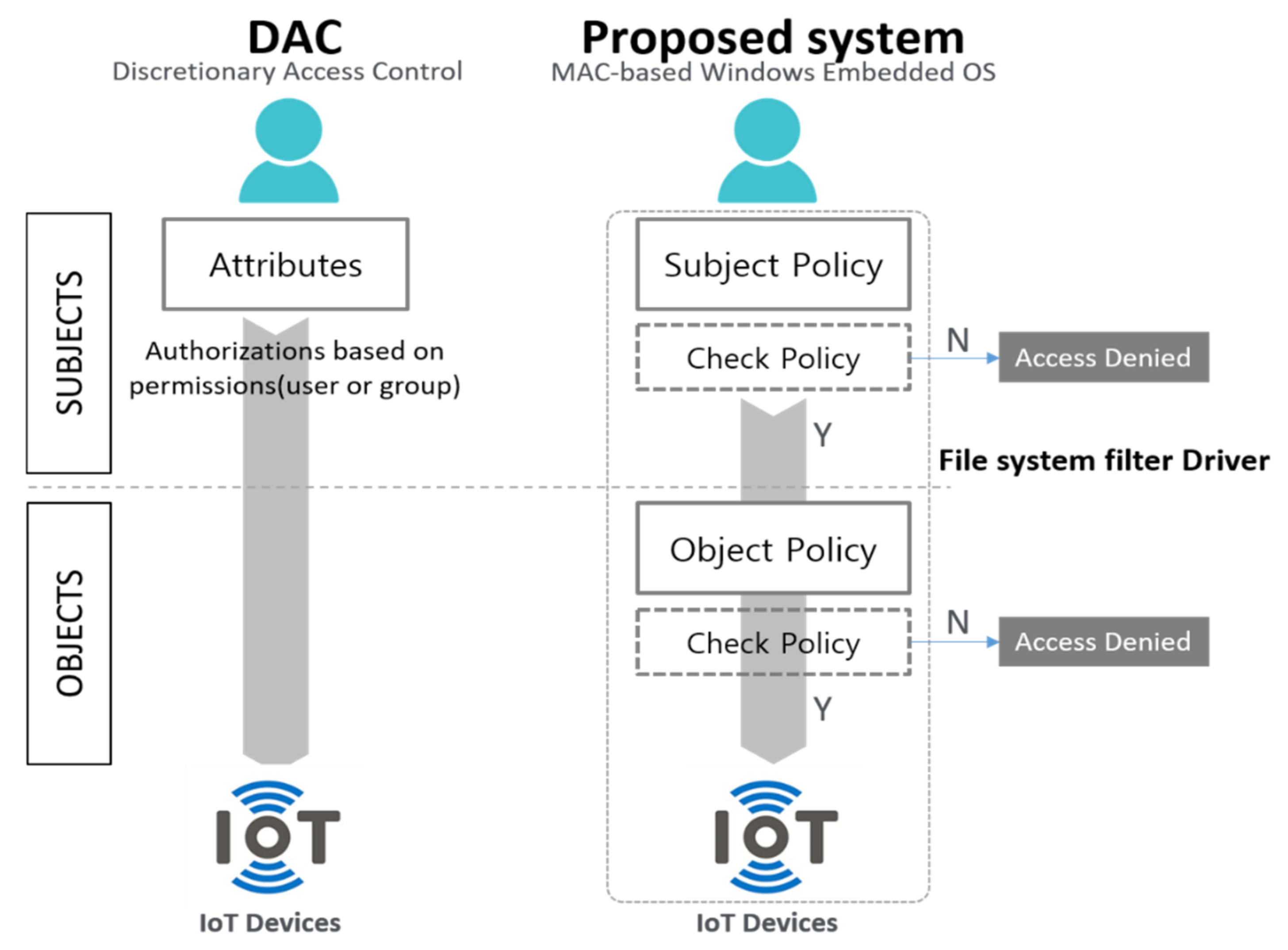
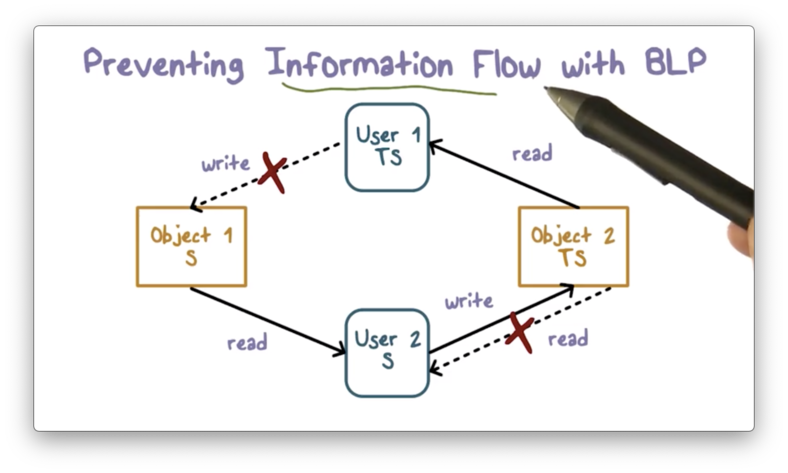
![PDF] Mandatory Access Control for Linux Clustered Servers | Semantic Scholar PDF] Mandatory Access Control for Linux Clustered Servers | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/a7b0ab92072ccfb1cb0a21081d0140517f417446/3-Figure1-1.png)








.png)